Json Web Token (jwt)
I think the main rationale for using JWTs is when you don’t want a large, multi-server application to rely on a centralized session storage server, which might be not fast enough, or is just out of scope/budget/requirements. Our maybe the application might not even be large, but just have the API on another domain and you don’t want to deal with cookies on multiple domains. Everything well explained in the article, anyway. I’ve never developed one so far, so I always relied on session cookies, but I’m open to (and curious about) the JWT approach. Olaiya segun paul wrote.
Some web applications today are using to improve perceived performance, by reducing the time to first render of real content. Unfortunately if you are using JWTs for authentication your initial request (from a browser at least) can’t provide the JWT unless it is stored in a cookie (and once you are storing it in a cookie you are losing some of the JWT benefits like cross domain request and resilience to CSRF) so you wouldn’t be able to provide SSR content for logged in users like you could with cookie sessions.
Perhaps a small trade-off, but one that can be overlooked when evaluating JWT vs Sesssions. Ifeora Okechukwu wrote. Okay you can have JWTs in cookies (which now gives you a signed cookie) and still use them cross domain (only as subdomains on a given host tho).
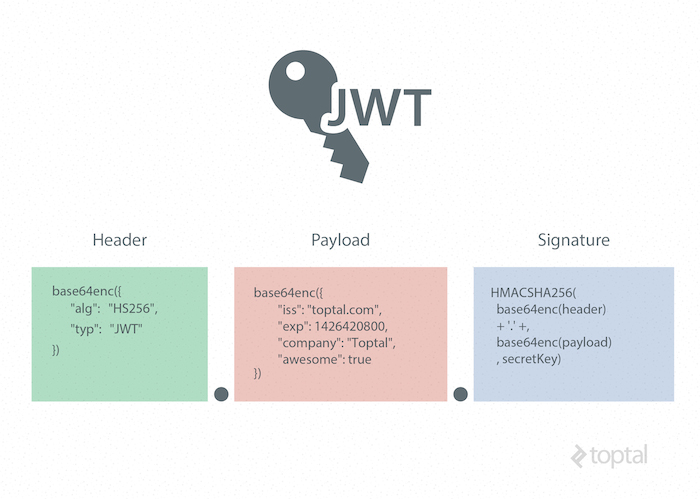
- A JSON Web Token (JWT) is a JSON object that is defined in RFC 7519 as a safe way to represent a set of information between two parties. The token is composed of a header, a payload, and a signature.
- JSON Web Token (JWT) is a compact URL-safe means of representing claims to be transferred between two parties. The claims in a JWT are encoded as a JSON object that.
Battle chess game of kings early access-tptb keygen software for mac. May 1, 2018 - Hello guys, not so long ago the concept of JSON Web Token was introduced and it became popular very fast and loved by many developers for.
Json Web Token (jwt)
Actually, the “trick” involved is what Google does while integrating with their different services. How do you think “” communicates with “” or “”? It’s by using cookies that have the “domain” field set to “.google.com” and “httpOnly” fields to “true”. The httOnly field protects against XSS. The JWT can also be sent with a custom X header Nonce value which the server can store to avoid replay attacks on that same. Alain Van hout wrote.
Thanks for the article, some great info in there. A couple of notes I had:. XSS can also compromise cookies (and not just Web Storage as mentioned in the article). In fact, one of the main goals of XSS is to steal someone’s session (or JWT) from their cookies, and send that info to the attacker to use. Unless JWTs are encrypted, there could be a lot of confidential info that can be stolen from the user owning or having a JWT.
Limiting JWT by IP might not be realistic if for example 10 users from a company X are using a site which issues JWTs (since company X uses NAT with a single public IP). How would JWTs work in that scenario? What about VPNs? Or a user who uses multiple WiFi hotspots and therefore multiple or different IPs? Not so practical. If JWTs expire within a short period of time (less than 1 hour), that would require the users to authenticate multiple times per day.
So we are effectively using JWTs in order to have a stateless interaction with the web server, but we are at the same time asking the user to login and maybe expose their credentials more frequently than using a Session ID. The more credentials that are sent over the wire (or WiFi) the more security risks are increased. Signing JWTs does not really solve the problem of replay attacks.
Sure the JWT is signed, but if I would like to have the same privileges and rights are the person I am stealing the JWT from, well, signing it would only guarantee that I can still do so if I have access to their JWT:) Perhaps the rest can be done after logging in to the application (changing passwords for instance). I believe once the JWT is encrypted, a lot of security risks are mitigated.
Replay attacks are very hard to deal with, especially if it is within the token’s valid time-frame, whether it is encrypted or not. Darragh wrote.
All of us know what happens if our user credentials (email and password) are discovered by an attacker: they can log into our account and wreak havoc. But a lot of modern applications are using JSON Web Tokens (JWTs) to manage user sessions—what happens if a JWT is compromised? Because more and more applications are using token-based authentication, this question is increasingly relevant to developers and critical to understand if you’re building any sort of application that uses token-based authentication.
To help explain the concepts fully, I’ll walk you through what tokens are, how they’re used, and what happens when they’re stolen. Finally: I’ll cover what you should actually do if your token has been stolen, and how to prevent this in the future. This post was inspired by this. My response to that question has become one of my most popular responses on StackOverflow to date!
What is a Token? A token in the context of web development is nothing more than an arbitrary value that represents a session. Tokens can be strings like “abc123” or randomly generated IDs like “48ff796e-8c8a-46b9-9f25-f883c14734ea”. A token’s purpose is to help a server remember who somebody is.
Take API services, for example: if you have an API key that lets you talk to an API service from your server-side application, that API key is what the API service uses to “remember” who you are, look up your account details, and allow (or disallow) you from making a request. In this example, your API key is your “token”, and it allows you to access the API. However, when most people talk about tokens today, they’re actually referring to JWTs (for better or ). What is a JSON Web Token (JWT)? Are special types of tokens that are structured in such a way that makes them convenient to use over the web. They have a handful of defining traits:.
They are represented as normal strings. Here’s a real JWT. EyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzdWIiOiIxMjM0NTY3ODkwIiwibmFtZSI6IlJhbmRhbGwgRGVnZ2VzIiwiaWF0IjoxNTE2MjM5MDIyfQ.sNMELyC8ohN8WFWRnRtdHMItOVizcscPiWsQJX9hmw Because JWTs are just URL safe strings, they’re easy to pass around via URL parameters, etc.
They contain JSON-encoded data. This means you can have your JWT store as much JSON data as you want, and you can decode your token string into a JSON object.

This makes them convenient for embedding information. They’re cryptographically signed. Understanding how this works is a.
For now, just know that it means any trusted party who has a JWT can tell whether or not the token has been modified or changed. This means if your application or API service generates a token that says someone is a “free” user and someone later alters the token to say they are an “admin” user, you’ll be able to detect this and act accordingly. This property makes JWTs useful for sharing information between parties over the web where trust is difficult to come. Here’s a small code snippet which creates and validates a JWT in JavaScript using the library. This example is purely here to show you at a glance how to create a JWT, embed some JSON data in it, and validate it.